SPRZ570A November 2023 – May 2024 AM263P4 , AM263P4-Q1
i2427
RAM SEC can cause Spurious RAM writes resulting in L2 & MBOX memory corruption
Details:
In case when a memory encounters a single-bit error during a RAM read data either due to a read or a partial write transaction, the RAM will enter a state which could lead to a later spurious write to the RAM if the next "memory read" is due to a subsequent partial write transaction. If the "memory read" is instead due to an actual memory read transaction, then the lingering bad internal state would be cleared and there wouldn't be any possibility of a later spurious write. The spurious write would be to the last memory address written prior to the partial write transaction which triggers the spurious write. The issue is only applicable to MBOX & L2.
Figure 2-2 lists possible scenarios where the issue is applicable (Example 1,2,3) and not applicable (Example 4,5,6) for more clarity. Transaction# are for illustration and doesn't necessarily represent the exact cycle each operation occurs. [SEC – Single bit Error Correction, DED – Double Bit Error Detection]
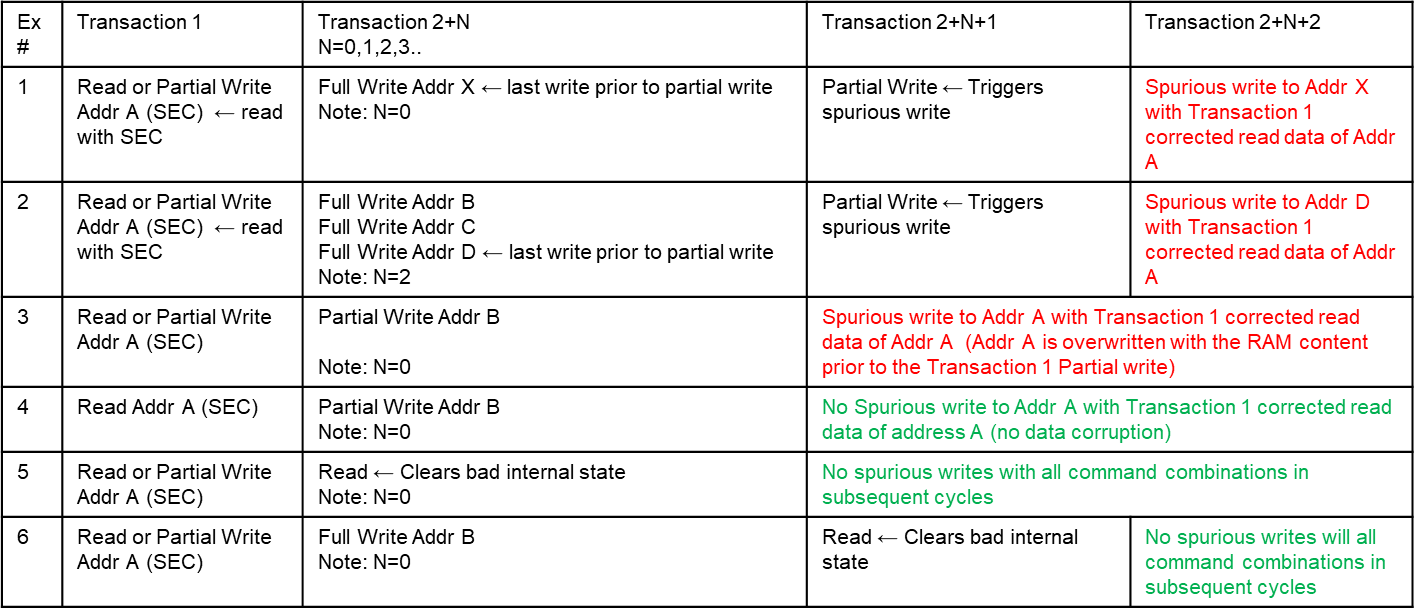 Figure 2-2
Figure 2-2 Workaround(s):
One of the below Options can be used as workaround.
Option 1:
Disable ECC, Applicable only for non-safety application.
Option 2:
Disallow Partial writes to the memory (only perform full line writes)
In case of L2, if the L2 space is cacheable the core will perform only full line writes and this issue is not applicable.
Option 3:
The application can treat all SEC errors like a DED (no correction only detection even in case of single bit error) since there is a possibility of RAM data corruption if application can't control the transactions immediately after a single bit error on a read or partial write transaction.